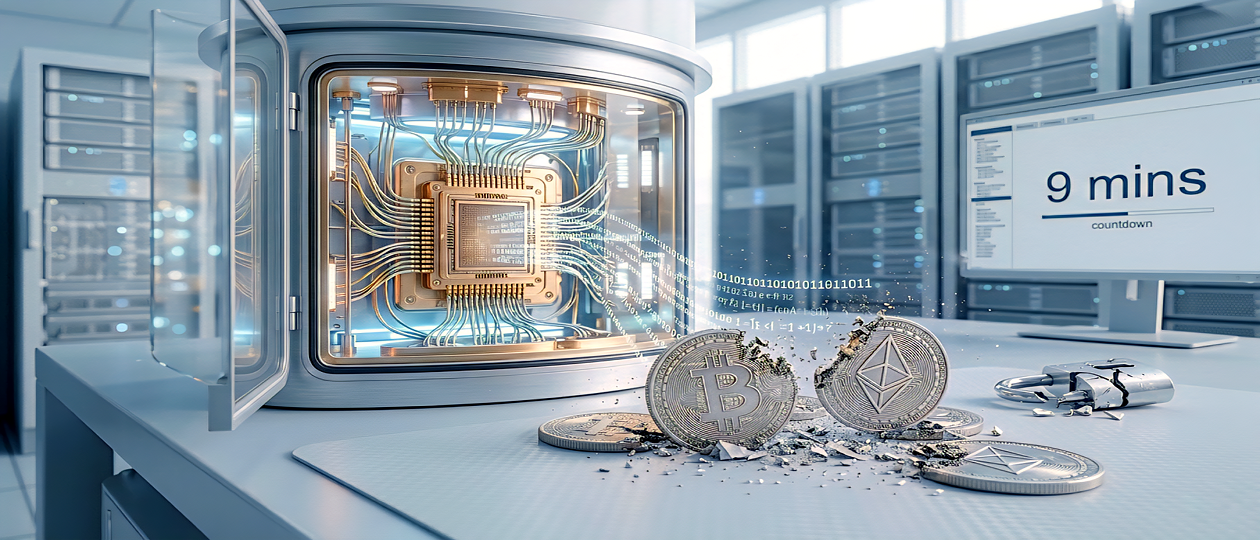
Mathematical Proof: Quantum Hacking is a Matter of minutes, not years.
In late March 2026, a groundbreaking report was published by a collaborative research group from Google Quantum AI, the Ethereum Foundation, Stanford, and Berkeley. Rather than issuing another abstract warning regarding the potential of quantum computing, the scientists provided a mathematically precise calculation. Their findings reveal that the window for compromising the world’s leading cryptocurrencies is no longer measured in decades, but in approximately 9 minutes.
Current blockchain security for networks such as Bitcoin and Ethereum relies upon the Elliptic Curve Digital Signature Algorithm (ECDSA). Conceptually, this functions as a mathematical lock that is effortlessly engaged—to create a wallet address—but remains virtually impossible for a classical computer to breach over billions of years.
However, quantum computers operate under a different set of computational principles. Utilizing Shor’s algorithm, these systems can bypass such locks by deriving a user’s private key directly from their public address. While discourse has long centered on the theoretical necessity of millions of qubits, this recent report from Google and its partners shifts the conversation toward engineering precision.
1,200 QUBITS TO CATASTROPHE
The primary conclusion of the study indicates that to fully compromise the “secp256k1» curve—the cryptographic foundation of Bitcoin and Ethereum—a quantum computer would require between 1,200 and 1,450 logical qubits. Previous estimates suggested a requirement of 317 million physical qubits; however, the significance of this document lies in the researchers’ ability to «compress» the algorithm.
According to the report, contemporary quantum architectures are capable of executing the decryption algorithm in a mere 9 minutes. In the cryptocurrency ecosystem, this introduces a critical «vulnerability window».
A user’s public key only becomes visible to the network at the moment a transaction is initiated. The transaction then enters the *mempool* (a queue), where it awaits confirmation by miners.
In the Bitcoin network, a new block is mined approximately every 10 minutes. This creates the threat of an «on-spend attack». The authors characterize this as a «Race Against the Block,» estimating the probability of a successful quantum theft at approximately 41%:
1. A user initiates a transfer.
2. An adversary detects the transaction in the queue.
3. Within 9 minutes, a quantum computer breaches the wallet.
4. The hacker generates a competing transaction to divert the funds to their own address, attaching a higher fee to ensure priority confirmation.
Approximately 2.3 million Bitcoins are currently held in «dormant assets,» including nearly 1 million coins belonging to the enigmatic creator of Bitcoin. For a quantum computer, these «cold wallets» represent «low-hanging fruit».
The authors also address the ethical and legal dilemmas regarding the ownership of these assets. A radical proposal suggests applying «maritime salvage law for sunken treasures» to these coins. Consequently, governments might initiate legal «hunts» for these billions under the guise of national security to prevent such resources from falling into the hands of illicit actors.
Furthermore, a significant crisis could emerge surrounding stablecoins—digital equivalents of the US dollar such as USDT and USDC. If a quantum computer were to compromise the keys of their administrators, attackers could generate trillions of fraudulent tokens, instantly collapsing the global DeFi economy. This «domino effect» would impact anyone utilizing modern banking applications.
TRUST, BUT VERIFY
The distinction of this report lies not only in its data but also in its methodology. The researchers employed a principle of «responsible disclosure». To validate their calculations without providing a functional «hacking recipe» for malicious actors, they utilized Zero-Knowledge Proof (ZKP) technology.
By employing the SP1 system, the researchers generated a cryptographic certificate. This allows experts to verify that the mathematical model and resource estimates are accurate while the specific attack «blueprints» remain shielded. It serves as a «gentleman’s warning» to the cryptographic community.
THE PATH FORWARD
The authors state that their proof remains valid until a Cryptographically Relevant Quantum Computer (CRQC) is fully realized. It is important to distinguish between physical and logical qubits. Current processors, such as the IBM Osprey (433 qubits) or Condor (1,121 qubits), utilize physical qubits which are «noisy» and prone to error. In contrast, logical qubits are error-corrected units composed of hundreds or thousands of physical qubits.
Between late 2023 and early 2024, researchers from Google and QuEra achieved a breakthrough by creating the first stable logical qubits. Moving from dozens of logical qubits to the required 1,200 is a significant distance; however, it is now viewed as a challenge of engineering scaling rather than fundamental impossibility. Given the current pace of development, a «universal skeleton key» for the creator’s wallets could emerge within the coming years.
The scientific community is calling for the immediate implementation of Post-Quantum Cryptography (PQC)—new algorithms designed to resist quantum attacks. Blockchains face a complex «open-heart surgery»: replacing fundamental signature protocols without halting networks valued in the trillions. Therefore, the authors insist that these defensive upgrades are required «yesterday,» as the transition for global networks may take years that the world might not have.